Bad Passphrase Try Again for homes jreh ssh id rsa
Last updated on 08/27/2020
This guide demonstrates how to setup automated OpenSSH RSA public-key authentication for Windows (using OpenSSH v3.8.1p1-1) and Linux (using OpenSSH v5.3p1) PCs currently working with password hallmark on a local network. The information for this guide was tested on PCs with WinXP and Lubuntu and may be applicable to other versions of Linux and Windows. You will demand physical access to both PCs.
Public-key Cryptography
Public-key cryptography uses of a pair of matching keys, a public cardinal and a private key, which are created at the aforementioned fourth dimension using a key generation utility (ssh-keygen.exe is the cardinal generation utility used in OpenSSH). A public central can be known to anyone and is used to encrypt data. The only way to decrypt information encrypted with the public key is with the matching private fundamental. Although the 2 keys are related, a private key tin't be created from its matching public key. Public-key cryptography is widely used for public-central hallmark to enable secure logins to servers without passwords and for digital or electronic signatures, and for certifying the authenticity of information signed by the private fundamental.
The importance for using pubic key authentication can be summed up in this statement from the Ubuntu aid pages: "If your SSH server is visible over the Cyberspace, y'all should use public cardinal authentication instead of passwords if at all possible. If you don't think it's important, try logging all of the malicious login attempts you go for the next calendar week. My computer – a perfectly ordinary desktop PC – had over iv,000 attempts to guess my countersign and well-nigh ii,500 break-in attempts in the final week lone."
OpenSSH Public-cardinal Hallmark
OpenSSH tin use either the RSA or DSA algorithms for public-key authentication. RSA stands for Rivest, Shamir and Adleman, the concluding names of the MIT team members who developed it. DSA stands for Digital Signature Algorithm, a US Regime standard proposed past the National Institute of Standards and Technology. Although there are arguments for and against using one or the other, RSA is ofttimes the preferred choice considering of its verification speed and central strength. See What is better for GPG keys – RSA or DSA? for a discussion on on this topic.
Steps for RSA Public-central Authentication
The post-obit steps will setup RSA public-fundamental authentication keys without a passphrase to enable automatic logins betwixt Linux to Windows PCs on a local network. The instructions volition be similar to setting up public-primal hallmark on remote hosts, except that SSH port 22 (if using the default port) must be forwarded to admission remote servers from behind a router. When creating keys without a passphrase, equally in this guide, make sure to place the public key on trusted hosts as it's possible to compromise the remote reckoner should your private fundamental autumn into the incorrect hands.
From the Windows PC
Footstep i – Generate Public Keys for the Windows PC
On the Windows PC, open a CMD window and type in the post-obit command and hit ENTER to create a RSA key of 2048-bits (the default). The -t option specifies the type of key:
ssh-keygen -t rsa
Annotation: If you get a command is not recognized error, your path is incorrect. In this case, change to the bin folder where OpenSHH is installed to run the command.
When the command is executed, yous will be prompted for a location to salvage the keys, and and so for a passphrase as shown below. Hit ENTER to have the default locations and to set NO passphrase.
Output:
Generating public/private rsa key pair Enter file in which to salve the key (/home/username/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter aforementioned passphrase once more: Your identification has been saved in /home/username/.ssh/id_rsa Your public key has been saved in /habitation/username/.ssh/id_rsa.pub
The public key will be saved equally .ssh/id_rsa.pub and your individual key saved as .ssh/id_rsa in your home folder. The home directory was setup for the user(s) when OpenSSH was installed and configured.
Step two – Transfer Public Cardinal to Linux PC
For the public key to be usable, it must be appended to the .ssh/authorized_keys file on the Linux figurer and/or on other hosts y'all log into. If an authorized_keys file does non exist in your Linux computer'south domicile .ssh directory, create information technology. Also create a directory named "otherkeys". The public key (catastrophe in .pub) should be copied to "/home/username/.ssh/otherkeys" on the Linux reckoner using a USB bulldoze, another medium, or remotely through Windows file sharing, SCP, or with SSH if information technology's already working. Make sure to just copy the primal and non move information technology.
After transferring the public key, at the Linux PC, open a concluding window or remotely connect to it and navigate to the .ssh folder in your home directory, and append the public central using the command beneath:
cat otherkeys/id_rsa.pub >> authorized_keys
Notation: the key can also exist cut and pasted into the authorized_keys file using a text editor
OR – remotely copying and appending the primal with SCP and SSH
To remotely re-create the public primal to the Linux PC using SCP, enter the following in a control window. Note that there is no command for appending to a file using SCP. You will be asked for your password to use SCP remotely from the Windows PC:
scp ~/.ssh/id_rsa.pub [email protected]:/.ssh/otherkeys/
log in to the Linux PC with SSH, cd to the .ssh folder and execute the post-obit command to append the key:
cat ~/.ssh/otherkeys/id_rsa.pub >> authorized_keys
Step 3 – Edit sshd_config
Open a command window and attempt to cosign automatically to the Linux PC from the Windows PC using SSH. Brand sure the SSH server was started on the Linux PC. It should work. If not, continue with the residual of this stride then recheck.
To troubleshoot the SSH public-primal cryptography authentication processes, you lot can use the verbose option switch (-v) in the ssh command when logging in:
ssh -v [email protected]
If authentication didn't work, goto the Linux PC and bank check that the permissions of the .ssh directory are set to octal 700. If not, employ the following command from the Linux PC to alter it:
# chmod 700 ~/.ssh/authorized_keys
If error messages were observed relating to the known_hosts file, find and delete the entries in the known_hosts file in the user .ssh directory of the Windows PC. The entries causing the errors will exist numbered in the mistake message. Subsequently deleting the offending entry in the known_hosts file, test again to determine whether y'all tin log onto the Linux PC without using a password.
After verifying yous tin log into the Linux PC without using a password, password authentication volition yet work should RSA not work for any reason, which is a security vulnerability. Password authentication tin can be turned off completely by changing the following entries in the etc/ssh/sshd_config file on the Linux PC. To use RSA authentication exclusively, brand the following changes to the sshd_config to forcefulness public-key authentication and disable password hallmark:
PasswordAuthentication no PubkeyAuthentication yes RSAAuthentication yep
Later on saving the file, restart the Linux PC SSH server using sudo /etc/init.d/ssh restart from a last on the Linux PC before logging in.
____________________________________________________________________________________
From the Linux PC
The steps are essentially the aforementioned as the previous steps with a few minor differences from the previous instructions
Step i – Generate Public Keys for the Linux Computer
From the Linux PC, open up a terminal and type in the post-obit control and hit ENTER to create a RSA primal of 2048-bits (the default). The -t choice specifies the type of key:
ssh-keygen -t rsa
When the control is executed, you lot will exist prompted for a location to save the keys, and then for a passphrase as shown below. Hitting ENTER to accept the default locations and to gear up NO passphrase.
Output:
Generating public/private rsa key pair Enter file in which to relieve the key (/home/username/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter same passphrase once more: Your identification has been saved in /home/username/.ssh/id_rsa Your public key has been saved in /home/username/.ssh/id_rsa.pub
The public fundamental will be saved as .ssh/id_rsa.pub and your individual key saved equally .ssh/id_rsa in your habitation folder.
Step 2 – Transfer Public Fundamental to Windows PC
For the public key to be usable, it must exist appended to the .ssh/authorized_keys file on the Windows computer, other Linux PCs, and/or other hosts yous log into. If the authorized_keys file does non exist in the user'southward Windows .ssh directory, create information technology. Also create a directory named "otherkeys". The public key (ending in .pub) should exist copied to "\habitation\username\.ssh\otherkeys" on the Windows computer using a USB drive, another medium, or remotely with file sharing, SCP, or with SSH if it's already working. Make certain to but copy the cardinal and not move it.
After transferring the public fundamental, at the Windows PC, navigate to the .ssh binder in your home directory, and append the public cardinal to the authorized_keys file using the control below:
copy /b authorized_keys + otherkeys\id_rsa.pub authorized_keys
Note: the key tin too be cut and pasted into the authorized_keys file using a text editor
OR – remotely copy the central using SCP and append it locally
To remotely copy the public primal from the Linux PC to the Windows PC with SCP, enter the following in a terminal window. Note that in that location is no command for appending to a file using SCP. You will exist asked for your password to use SCP remotely from the Linux PC. (Note that Windows doesn't provide a way to easily suspend the public key remotely to the authorized_key file from the command-line)
scp ~/.ssh/id_rsa.pub [email protected]:.ssh/otherkeys/
This copies the public fundamental to the otherkeys folder.
Physically log into the Windows PC and employ an editor such every bit notepad or another app to append the key into the authorized_keys file.
OR – remotely re-create the key using SCP to overwrite the authorized_keys file (circumspection: this overwrites the authorized_keys file. Use only if the authorized_keys file is empty or if information technology doesn't matter if previous content is lost!)
execute the post-obit to overwrite the authorized_keys file with your public primal:
scp ~/.ssh/id_rsa.pub [electronic mail protected]:.ssh/authorized_keys
Step 3 – Edit sshd_config
In a terminal window attempt to log into the Windows PC with public-primal authentication using SSH. Brand sure the SSH server was started on the Windows PC. It should work. If not, continue with the rest of this step and so recheck.
To troubleshoot the SSH public-key cryptography authentication processes, you can use the verbose pick switch (-v) in the ssh command as follows when logging in:
ssh -v [email protected]
If mistake letters errors were observed relating to the known_hosts file, observe and delete those entries in the known_hosts file in the user .ssh directory in the Linux PC earlier continuing. The entries causing the errors will be numbered in the error message.
Later on deleting the offending entry in the known_hosts file, examination once more to determine whether y'all can log onto the Windows PC without using a password.
After verifying you can log into the Windows PC without using a password, password authentication volition still piece of work should RSA not work for any reason, which is as well a security vulnerability. Password hallmark can be turned off completely by changing the following entries in the OpenSSH\etc\sshd_config file on the Windows PC. To utilize RSA authentication exclusively, make the following changes to the sshd_config file to forcefulness public-key authentication and disable password authentication:
Note: If you still are unable to log in with pubic-key hallmark at this indicate, do not make the following changes to the sshd_config file to forcefulness public-key hallmark since y'all may need to login locally using your password with tools such as WinSCP. See below troubleshooting procedures:
StrictModes no PasswordAuthentication no PubkeyAuthentication yes RSAAuthentication yes
Subsequently saving the sshd_config file, restart the Windows PC SSH server outset by stopping it using net stop opensshd then restarting it using net first opensshd in a control window on the Windows PC to let the config file to take effect earlier logging in.
If public-key hallmark still doesn't work, the most likely cause is that that the read/write/access permissions for the .ssh directory or for OpenSSH for the Windows PC are incorrect. See the below troubleshooting procedures beneath for further information.
Troubleshooting Windows OpenSSH server issues:
File permissions issues are a notorious problem for getting public-key authentication to work for OpenSSH on Windows. It'due south probably the most confusing and almost hard issue to resolve. After much research and troubleshooting, I got information technology to work following this source from osdir.com. However, it's uncertain whether information technology was one, all, or a combination of the suggestions that stock-still the problem. In whatsoever case, below is a summary of the suggestions and how they were followed.
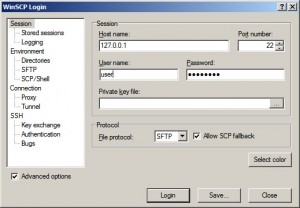
The tool used to modify file permissions for the instructions below was WinSCP, with 127.0.0.1 as the host name and SFTP as the protocol (encounter screenshot below).
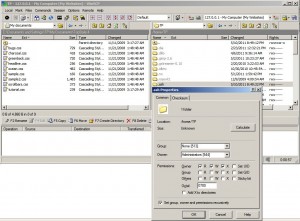
Permission changes were made using the properties window as shown in the screenshot below:
Here are the suggestions from osdir.com and how each was followed. Suggestions are preceded by an asterisk "*" and how the suggestions were followed are in bold :
*Change ownership of OpenSSH binder/subfolders to Administrators using Windows Explorer – Performed this for the folder and all subfolders using WinSCP.
*Grant Administrators full control of the OpenSSH folder – Same as higher up using Octal 0700
*From a command prompt, blazon "cacls c:\program files\openssh /t /e /c /yard Administrators:F" * – Performed this for the c:\ssh folder, which was the OpenSSH folder on my PC.
Edit sshd_config file and set StrictModes to "no" – Changed the StrictModes entry to "no" and saved the file
*Under the user'south profile, grant Administrators (and only Administrators) total control of the .ssh folder and files – Did this for all folders and files for .ssh in the user directory (C:\Documents and Settings\user\.ssh).
*If this folder does non be, it can be created past establishing an SSH connection to another box – Skipped. The .ssh file already existed
*On clients only, re-create the private RSA primal to the local .ssh folder and proper name information technology "id_rsa" – Skipped. The individual keys already existed.
*Copy the client'south public RSA key to the desired server(southward) by adding it to an "authorized_keys" text file located nether the server'due south .ssh binder – Skipped. Done previously.
* To utilize publickey authentication, use the SSH control line switch "-o PreferredAuthentications=publickey". Alternately, you can modify the ssh_config file to make this the default – Skipped.
If the to a higher place instructions worked:
Determine whether to apply RSA authentication exclusively. If so, edit the sshd_config file per the instructions above.
Notation: many instructions on various web sites suggest copying public keys to the user's .ssh directory on the server. If you exercise, brand sure to place them in a separate folder such every bit a otherkeys folder or some other name such as username_key since existing public keys (id_rsa.pub) volition exist overwritten if multiple PCs are used to admission the aforementioned motorcar.
If you have plant a spelling error, please, notify the states by selecting that text and pressing Ctrl+Enter.
halvorsenwitoomards.blogspot.com
Source: https://cects.com/openssh-rsa-authentication-for-windows-and-linux/

0 Response to "Bad Passphrase Try Again for homes jreh ssh id rsa"
Publicar un comentario